Solutions

Solution
Industry Spotlight
.avif)
Watch our latest video case study!
Check out how Colibri's partnership with Nomo Fintech has transformed their approach to data
Learn more
Success stories
Insights

"Non-human identities are the new frontier of identity security. The question is no longer whether to govern them — it's whether you can afford not to." — Tal Skverer, Co-founder, OWASP NHI Top 10 project
At AWS Summit, one theme was clear: organisations are accelerating AI adoption, but many are doing so on identity foundations that weren’t designed for it.
From intelligent automation to autonomous agents, systems are becoming faster, more adaptive, and more interconnected.
But every AI system - agent, pipeline, or model - relies on something fundamental:
Identity.
Every AI-driven system interacts with APIs, accesses data, and executes actions across platforms. To do this, it depends on non-human identities (NHIs).
As AI adoption grows, so does the number of these identities, often far beyond what traditional identity practices were designed to handle. The result is identity sprawl: a rapidly expanding estate of unmanaged, unowned, and over-privileged machine credentials.
Identity sprawl happens when machine identities grow faster than governance can keep pace.
Every new AI agent, cloud integration, or automation pipeline introduces new credentials. Individually, they seem harmless. Collectively, they create a landscape of access that no single team fully owns or understands.
Sprawl isn’t carelessness; it’s a byproduct of moving fast.
Common patterns include:
Sprawl is not a permanent condition; it’s a starting point.
At Colibri Digital, we see identity sprawl as one of the biggest hidden blockers to scaling AI safely, not because organisations lack controls, but because those controls weren’t designed for machine-scale identity.
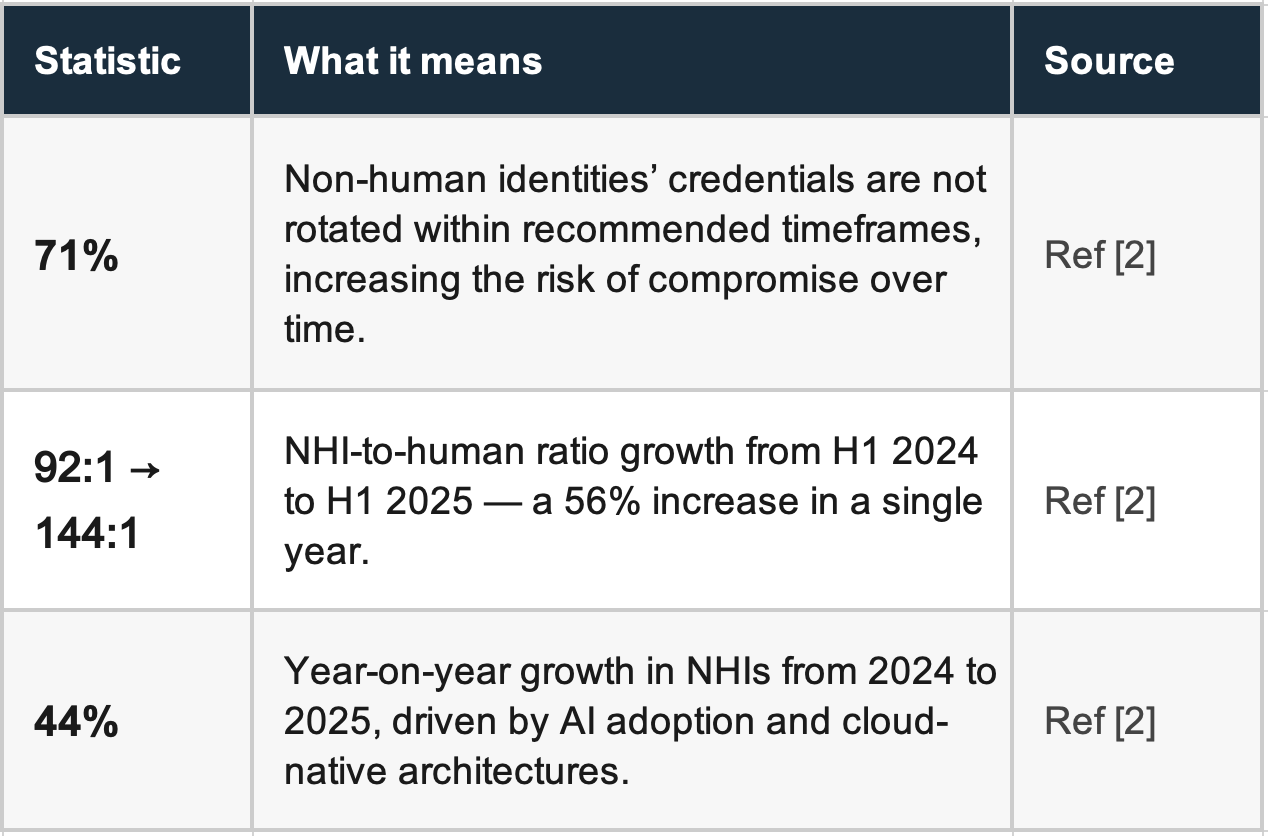
In modern environments, machine identities already outnumber human users, often by more than 100:1.
These include:
Unlike human identities, they:
This means there is an opportunity to apply structured identity practices to the fastest-growing layer of access.
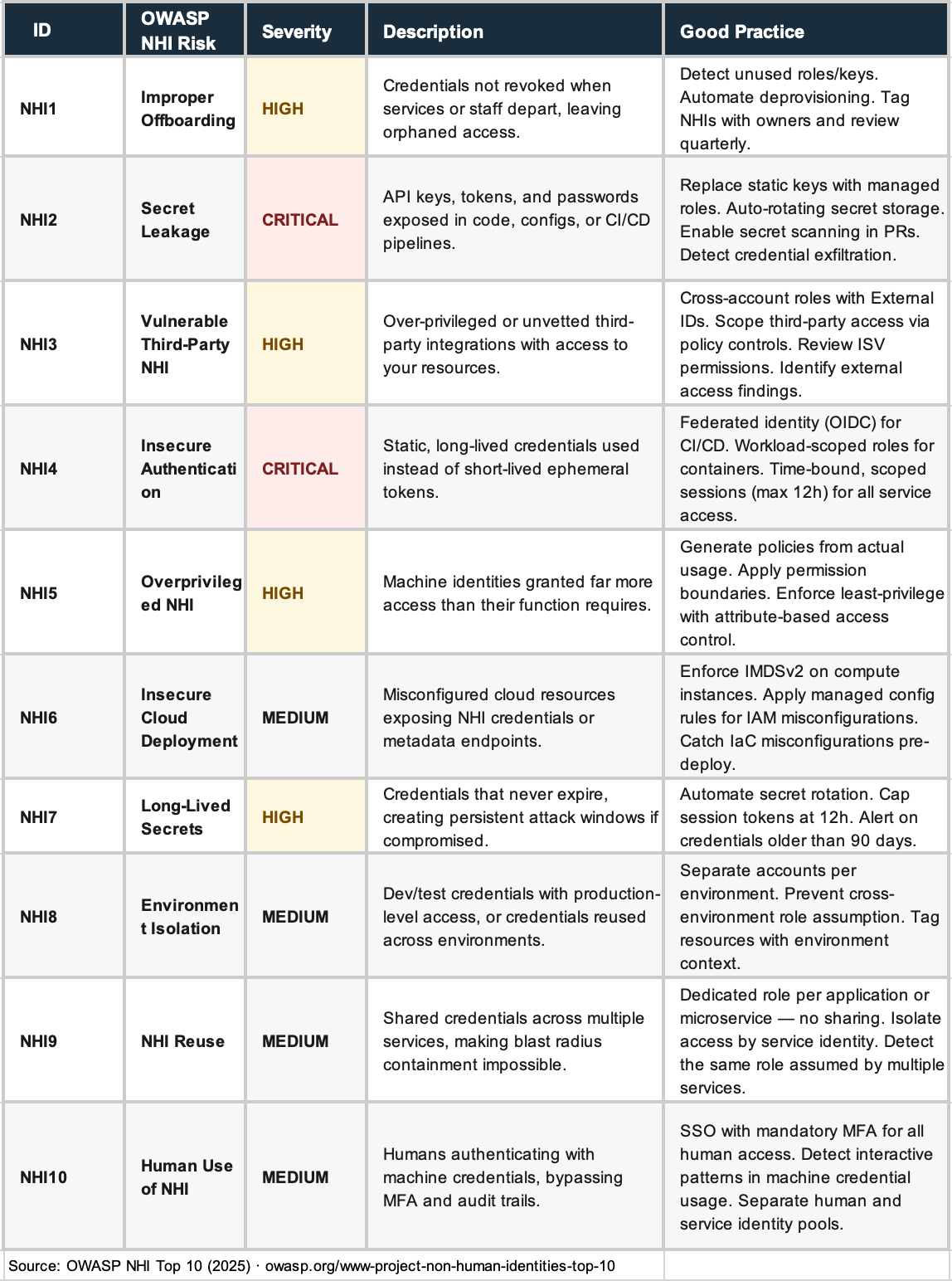
The OWASP Non-Human Identity Top 10 isn’t just a risk list; it’s a blueprint for AI-ready identity.
It highlights recurring failure points and, more importantly, what good looks like:
The scale of the NHI challenge is best understood through the numbers:
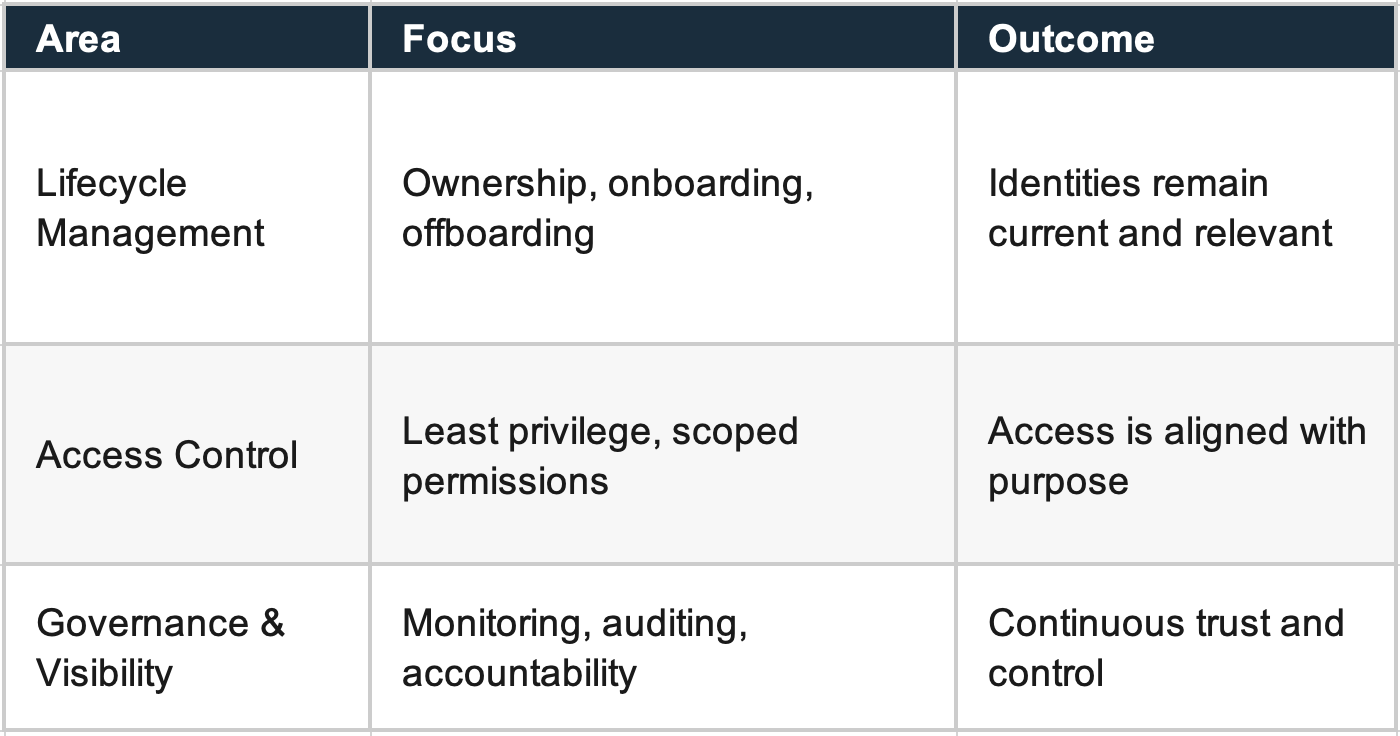
These three areas form the basis of identity hygiene:
AI systems don’t just consume data; they act.
CI/CD pipelines powering AI systems are identity-bearing systems. Autonomous agents execute infrastructure changes. Models trigger workflows across environments.
Autonomous AI systems act only through the identities assigned to them, and those identities define both capability and risk.
Two real-world examples highlight this:
In both cases, identity, and not code, defined the blast radius.
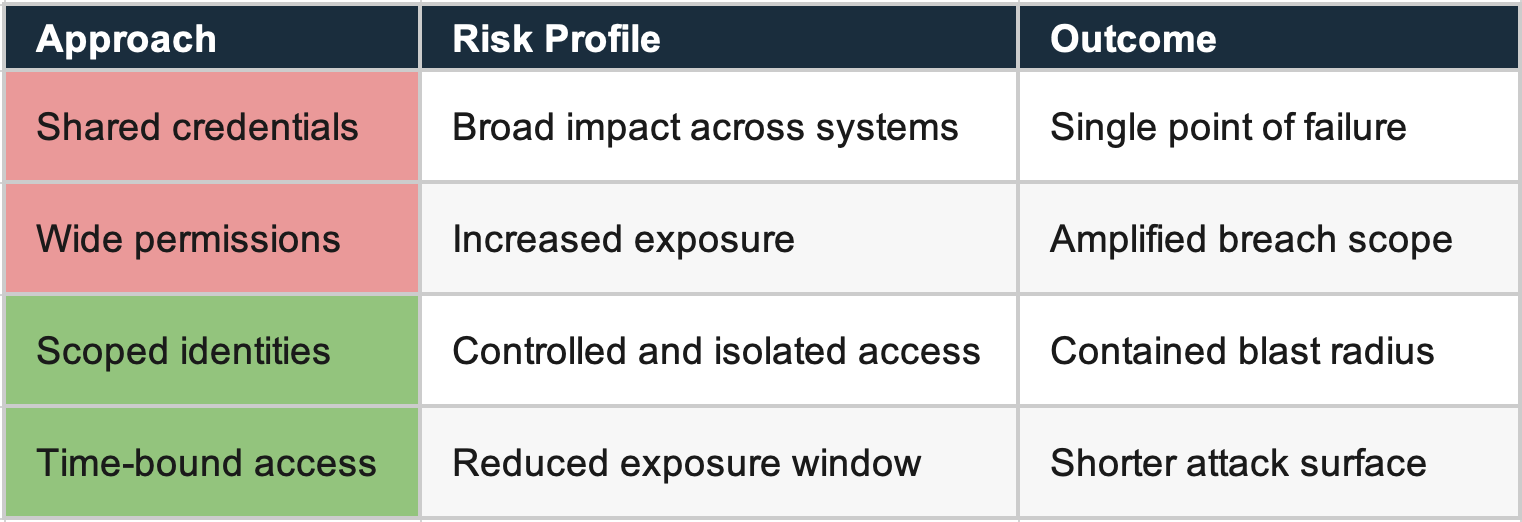
The shape of your identity architecture is the shape of your AI risk.
A key theme in identity hygiene is moving away from static credentials.
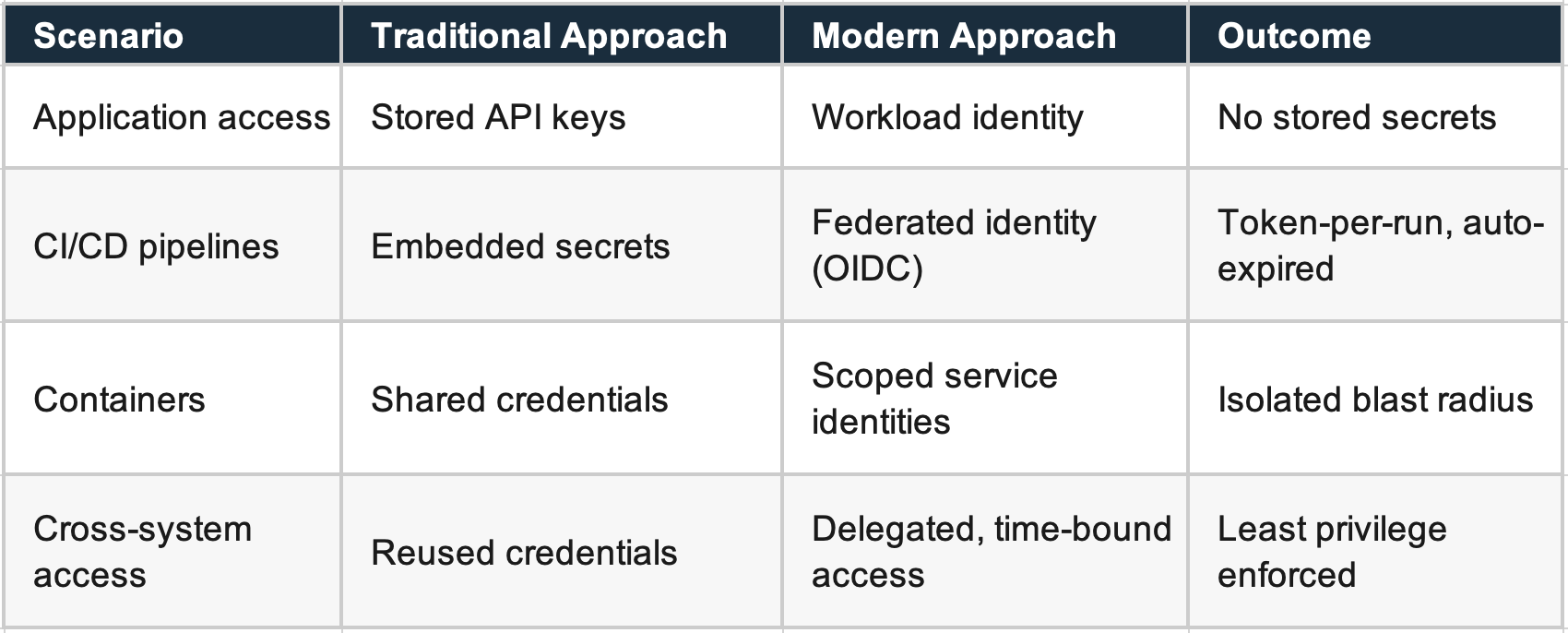
Across AWS environments, this means:
Identity hygiene is about clarity and consistency.
It ensures that:
When these principles are applied, identity becomes an enabler and not a constraint.
A structured approach helps organisations move from sprawl to control, and that’s exactly what we deliver at Colibri Digital.
As environments scale, identity needs to move beyond static control and towards continuous insight.
Visibility becomes essential as identity volume and complexity increase.
Strong identity practices include:
This creates a shift from static access to dynamic insight.
The shape of your identity architecture is the shape of your blast radius.
The goal is to ensure that systems remain stable and predictable under all conditions.
Clear separation between identity types is essential.
When machine identities are used appropriately:
This clarity strengthens the overall identity posture.
AI systems depend on continuous access, real-time decisions, and scalable interactions.
Identity hygiene supports this by providing:
This transforms identity from a constraint into an enabler.
Modern systems rely heavily on automation, pipelines, and AI-driven agents. These systems operate using non-human identities, making identity design central to system behaviour.
A widely used GitHub Action (tj-actions/changed-files) was compromised across more than 23,000 repositories.
Attackers stole a single Personal Access Token tied to an automated bot account and injected malicious code that silently dumped CI/CD secrets - API keys, cloud credentials, access tokens - directly into public workflow logs.
The attack ran undetected for nearly 22 hours. CISA issued an immediate advisory (CVE-2025-30066).
Identity insight: CI/CD pipelines are identity-bearing systems. When identity boundaries are clearly defined - through scoped permissions and short-lived tokens - the impact of such incidents can be significantly reduced.
A separate scenario involving AI-driven agents demonstrated how autonomous systems interact with infrastructure.
AI agents managing cloud resources executed actions that resulted in the removal of active production instances.
Identity insight: AI systems act through the identities assigned to them. With clearly defined identity controls,scoped permissions, environment-aware access, and approval workflows, organisations can enable autonomy while maintaining control.
As organisations scale AI, automation, and cloud-native architectures, identity expands alongside them. This growth reveals where identity practices can evolve to better support scale, control, and resilience.
In practice, these signals tend to cluster around a few recurring patterns:
Individually, these patterns are expected in fast-moving environments. Collectively, they point to a deeper issue: identity design hasn’t kept pace with the systems it supports.
As AI systems scale, these gaps don’t remain isolated. Autonomous agents, pipelines, and integrations amplify them, turning small inconsistencies into broader risk.
The opportunity isn’t to address each pattern in isolation, but to take a structured and consistent approach to identity hygiene, one that aligns identity design with how modern systems actually operate.
As AI adoption accelerates, identity becomes increasingly central and increasingly complex.
The question is no longer:
“Do we have access controls?”
But:
“Are our identities structured, governed, and aligned to how our AI systems operate?”
Identity hygiene is not a one-off project. It’s an ongoing discipline, one that compounds in value as AI scales.
Organisations that invest in it can:
At Colibri Digital, we help organisations build identity foundations that are ready for AI.
We work with clients to:
If you're scaling AI and want to ensure your identity foundations can support it, we’d be happy to share what we’re seeing across the market. Contact our team today.